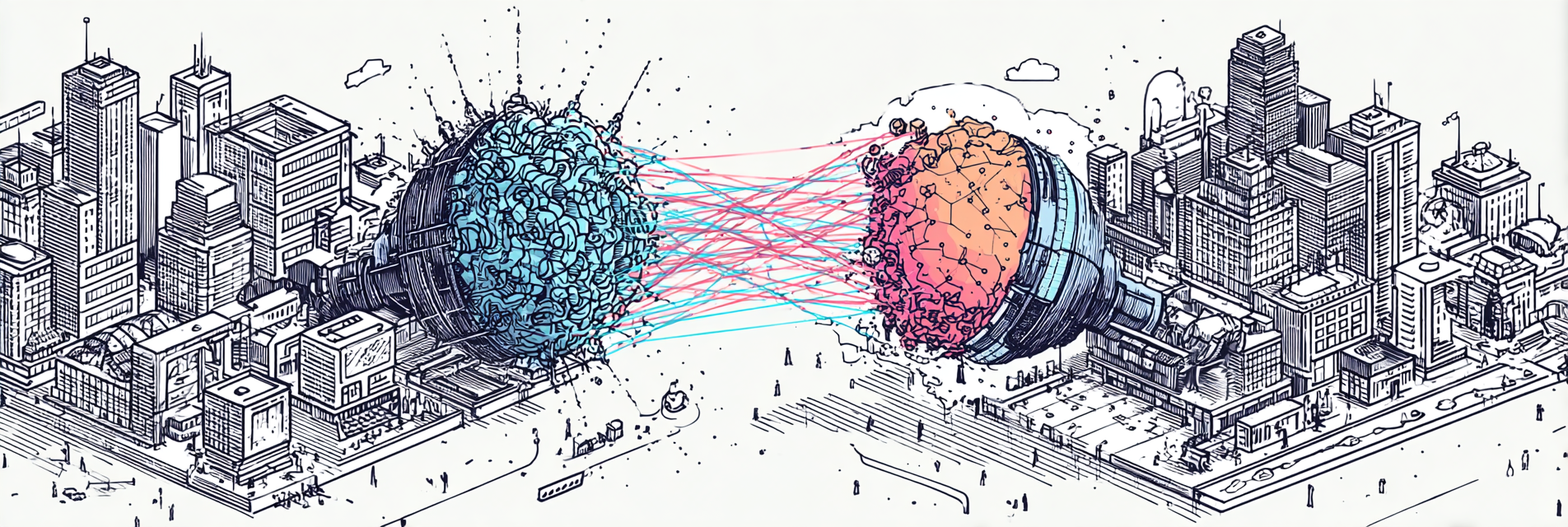
Two Paths for Encrypted Computation
CKKS vs. TFHE
CKKS
- Ideal for AI workload.
- Excels for data-heavy tasks.
- Parallelized operations on multiple values.
- GPU‑accelerated.
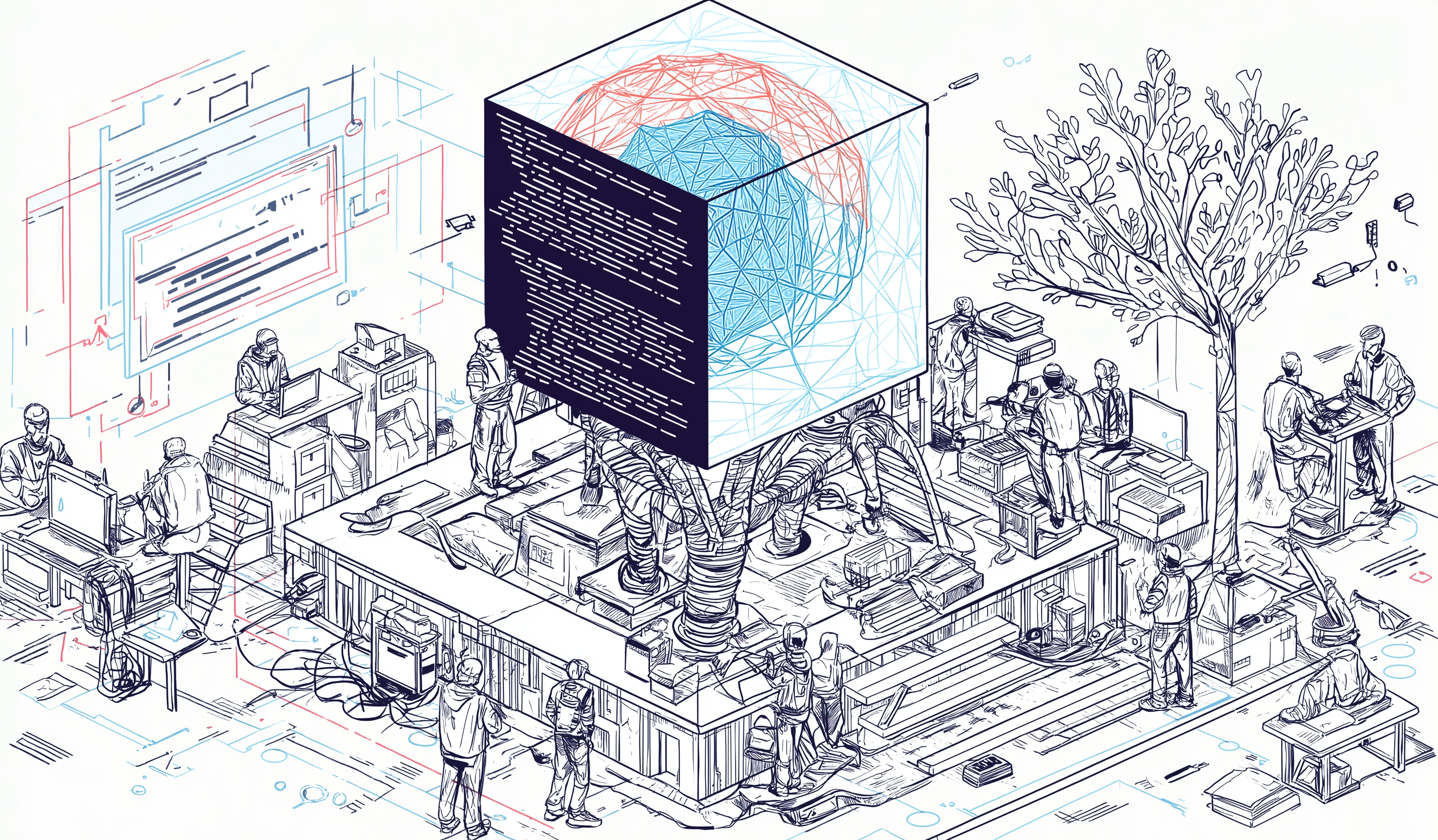
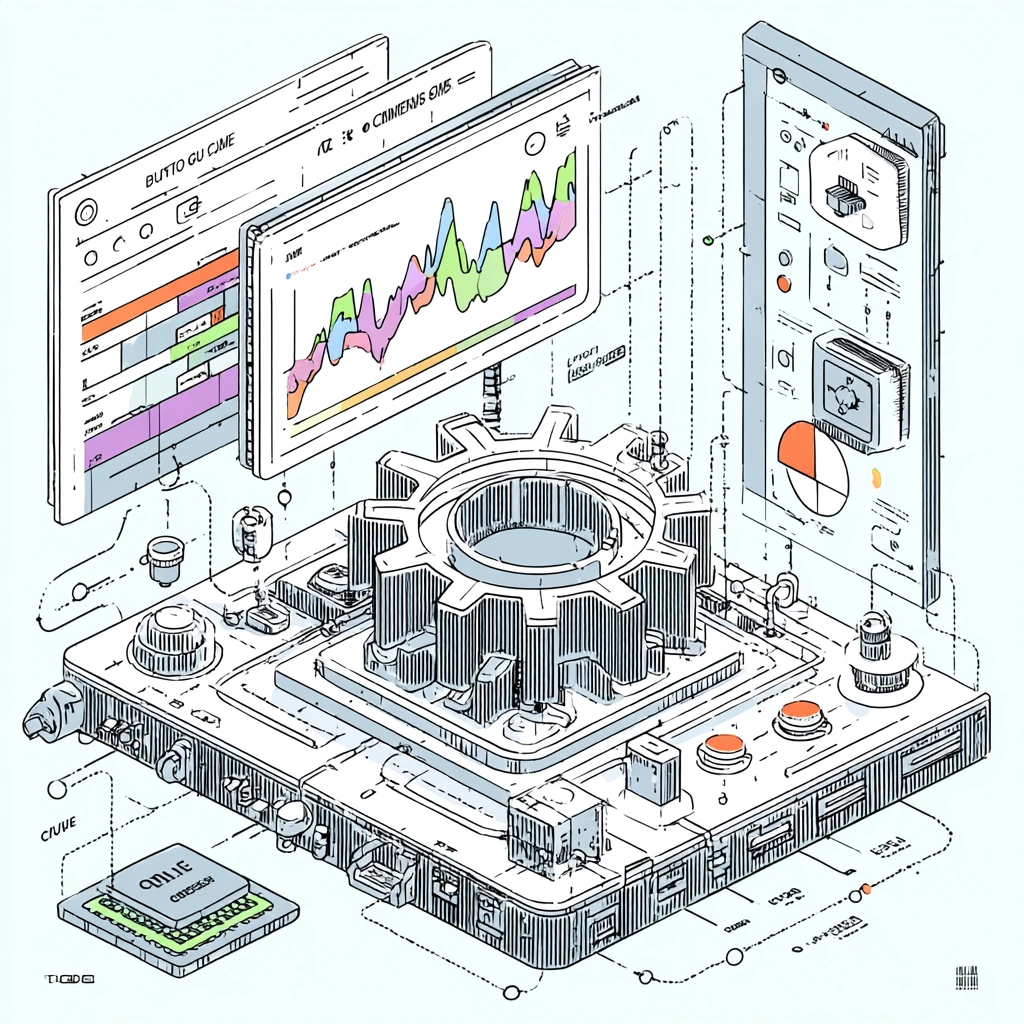
FHE Applications
FHE Software Stack
Algorithms
Core Building Blocks
TFHE
- Ideal for secure voting or blockchain logic.
- Excels at exact computation.
- Bootstrapping by design.
- CPU-based.
Under the Hood: Sunscreen and Lattica
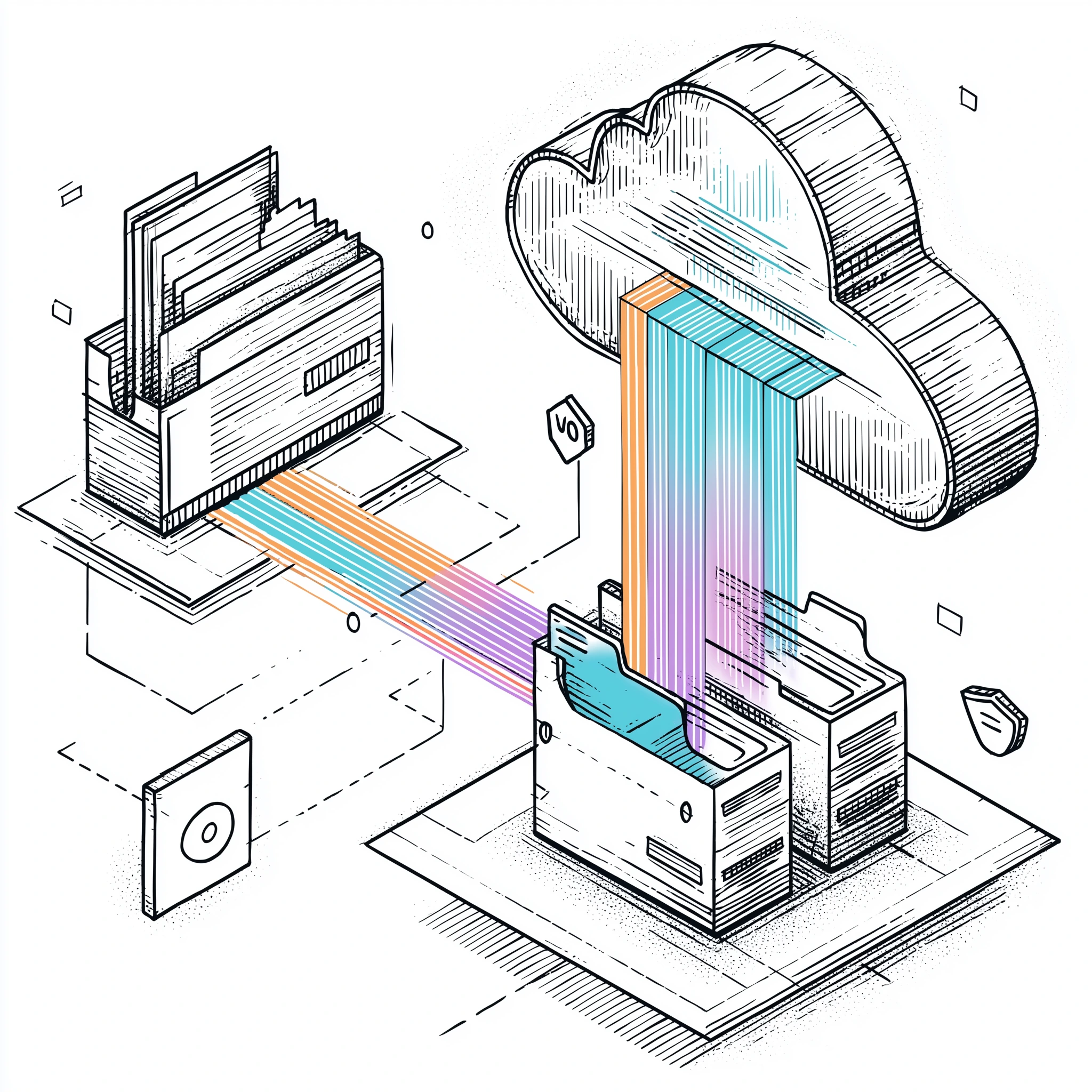
Deploys and Operates
- Orchestration and workflow automation
- Query Clients
- Computer resource allocation
- Management and monitoring
Sunscreen Compiler
Compile your program


Lattica
Management Client
-
Create a key set
-
Encrypt
-
Decrypt

Deploy Compiled Program

Deploy Evaluation Key

Encrypted Query

Encrypted Response
TFHE Engine
(Cloud)
The TFHE Engine
- Encrypted computation at the language and compiler level: TFHE Compiler (Parasol)
- TFHE runtime for encrypted programs
- See Sunscreen demos...
Get Started
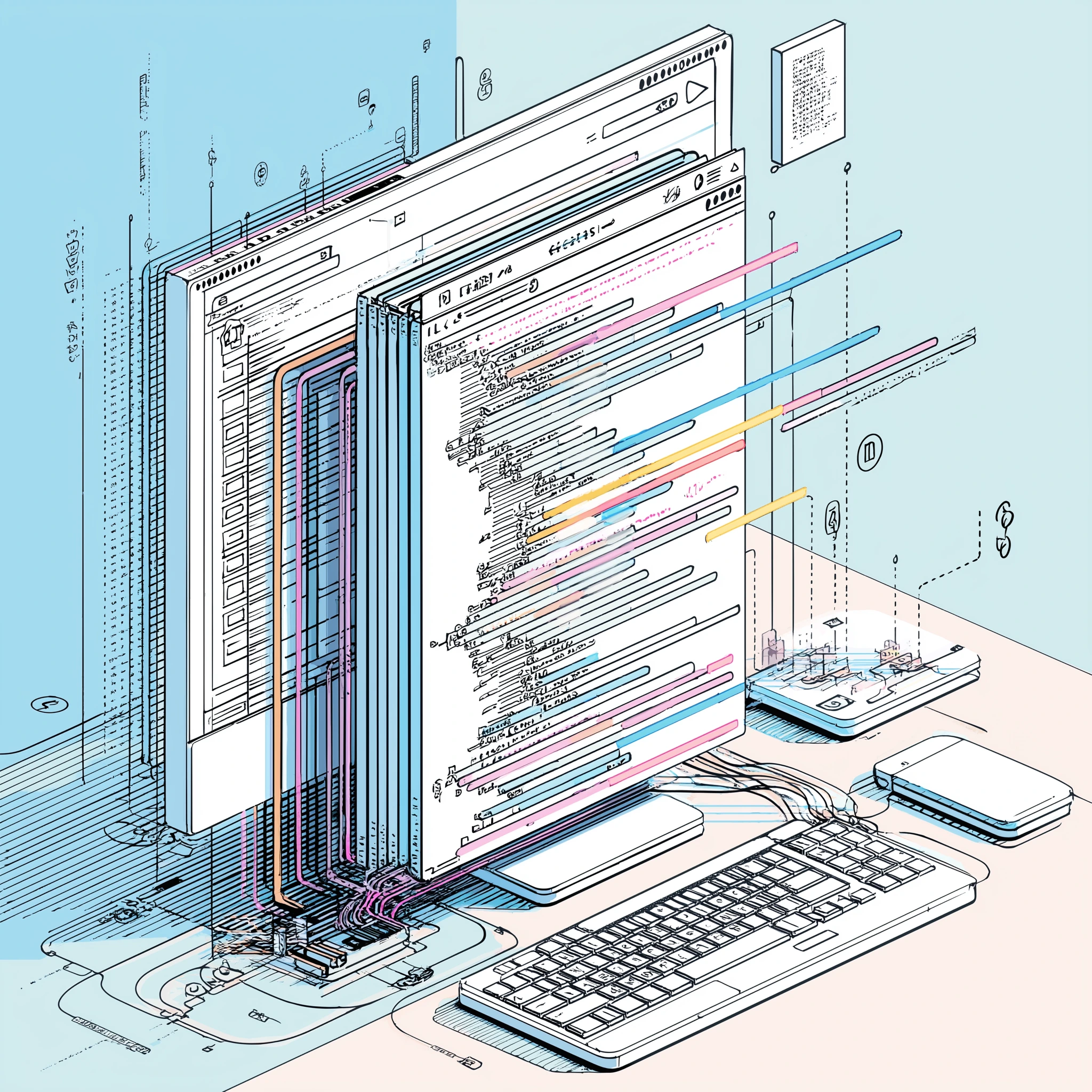
Compile with Sunscreen
Deploy your compiled program
Configure access and resources
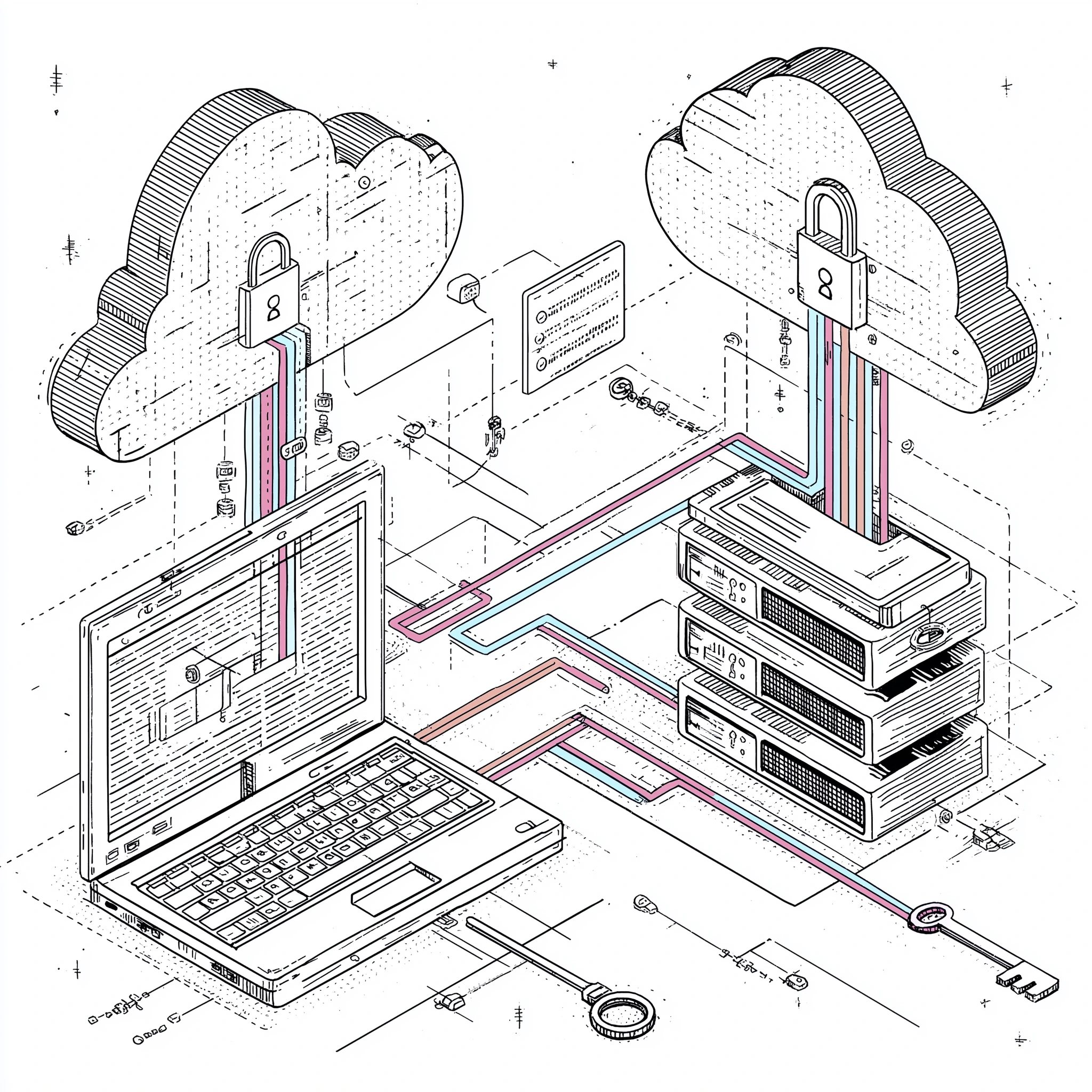
Your program is now ready for use
TFHE and CKKS are commonly used names for a family of FHE algorithms.